Unless you’ve been traveling without internet connectivity and access to newspapers, you must have heard about the recent ransomware which was propagating based upon a Microsoft Windows SMB bug. This is a quick blog with the information you need to validate that your 2008 and 2008R2 servers are not vulnerable to the exploit.
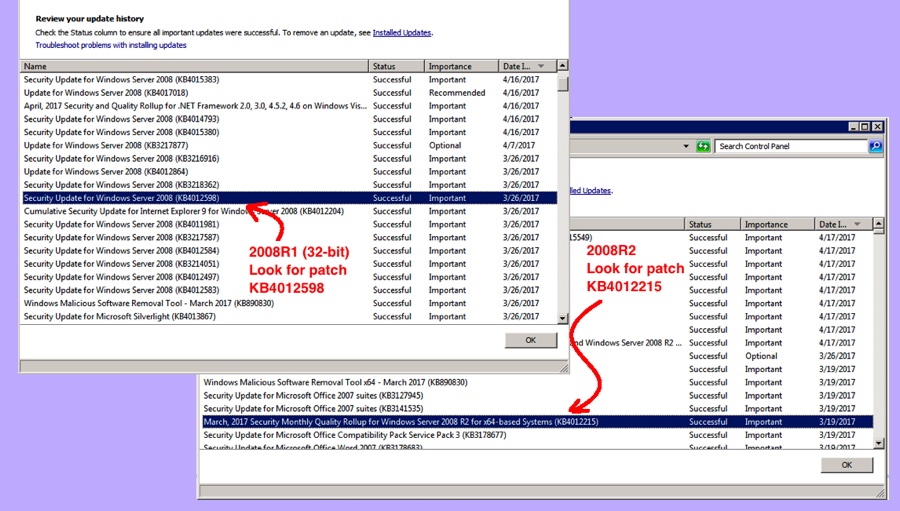
For 2008 32-bit, the patch is KB4012598. For 2008R2 64-bit, the patch is KB4012215. To check whether a particular patch is installed:
- Run Control Panel | Windows Update
- Click “View Update History” on the left
- Look for the KB patch number
If you don’t find the patch, or have a different Windows operating system, you can go here to download the proper patch:
https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
Since the patch was included in the March 2017 release of critical updates, you can also just run all patches on your server(s) to get the necessary update. However, be warned that patching is taking longer than normal right now, so you need to be patient. So, downloading the patch once, and then moving the patch file between servers is going to be significantly faster than allowing each server to reach out to Microsoft.